08
Scaling Your Security | The Ultimate Cybersecurity Tool Stack Maturity Model
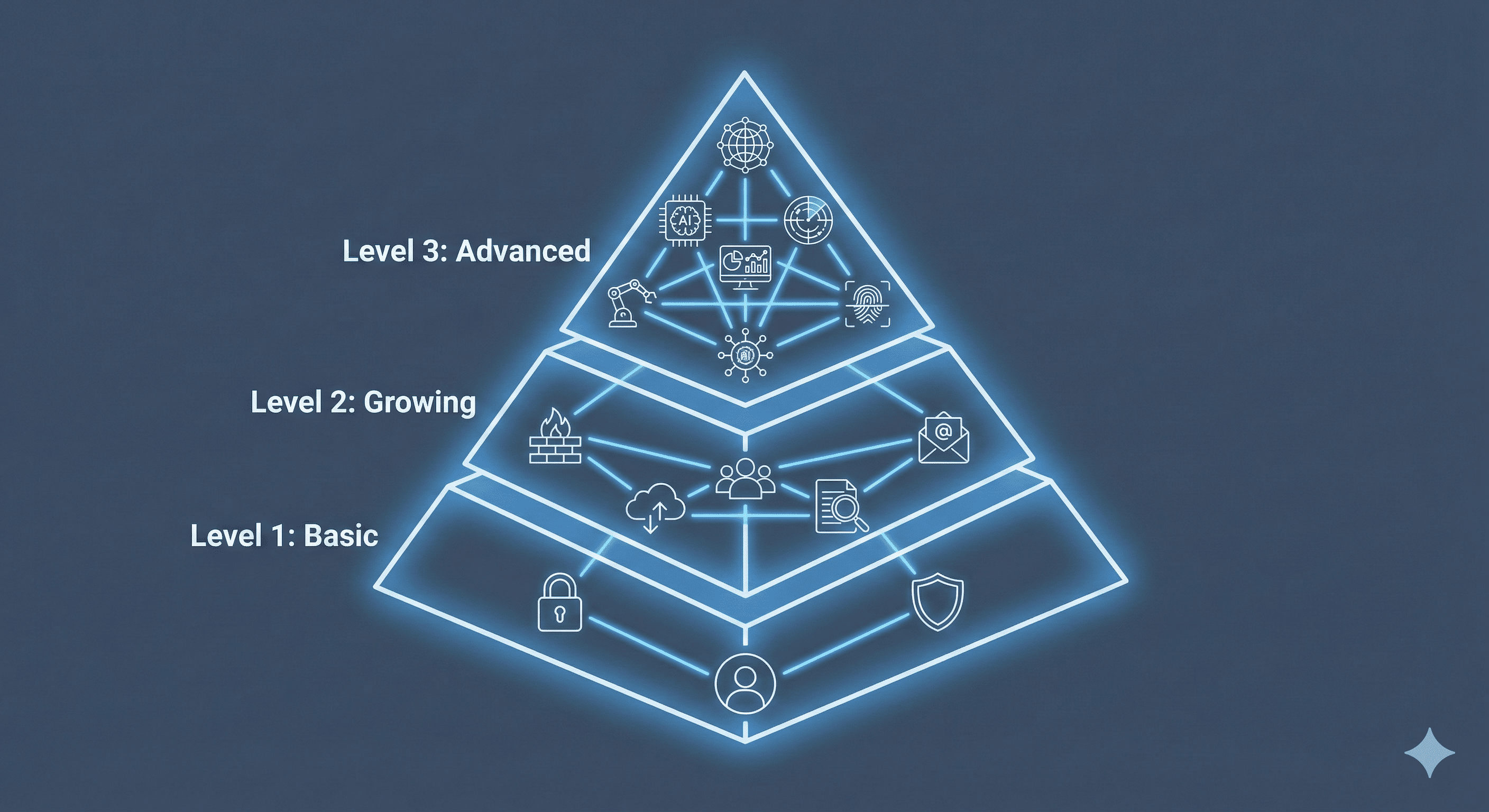
Security isn't one-size-fits-all. This guide uses a "crawl, walk, run" maturity model to explain the essential cybersecurity tool stacks for small teams, growing SMBs, and fully mature enterprises, focusing on when to add tools and how they integrate.
Scaling Your Security: The Ultimate Cybersecurity Tool Stack Maturity Model
One of the most paralyzing questions for IT leaders and business owners is: "Do we have enough security?"
The cybersecurity market is flooded with acronyms—EDR, XDR, SIEM, SOAR, ZTNA. It’s easy to feel like you need to buy everything immediately to be safe. But trying to implement an enterprise-grade security stack in a ten-person startup is like buying a Ferrari to learn how to drive: expensive, overwhelming, and likely ineffective.
Cybersecurity is a journey, not a destination. It requires a maturity model—a "crawl, walk, run" approach where you build a solid foundation before adding complex layers.
This guide breaks down the cybersecurity tool stack into three stages of maturity, helping you visualize where you are today and what your next strategic investment should be.
Level 1: The Basic Stack (The "Crawl" Phase)
Target Audience: Startups, Small Teams (1–50 employees), Low IT budget.
The Goal: Establish hygiene and block low-effort, untargeted attacks.
At this stage, you are likely not being personally targeted by nation-state hackers. You are targeted by automated bots looking for easy openings—weak passwords, unpatched software, and gullible employees. The goal here is to lock the doors and windows.
The Essential Tools:
- Next-Gen Endpoint Protection (NGAV/EDR):
- You cannot rely on Windows Defender alone. You need protection that uses AI to spot suspicious behavior, not just known virus signatures.
- The Function: Stops malware and ransomware on laptops and servers.
- Business Password Manager:
- Humans are terrible at creating passwords. A password manager ensures every employee uses unique, complex credentials for every service, eliminating the risk of credential stuffing attacks.
- The Function: Securely generates and stores credentials.
- Multi-Factor Authentication (MFA):
- This is non-negotiable. Even if a password is stolen, MFA prevents a takeover. Turn it on for email, file storage, and any critical business application.
- The Function: Verifies identity with a second factor (like a phone push).
- Automated Cloud Backup:
- Your ultimate insurance policy against ransomware. If everything else fails, you must be able to restore your data from a clean source.
- The Function: Creates recoverable copies of data offsite.
Level 2: The Growing Stack (The "Walk" Phase)
Target Audience: SMBs, Mid-Market (50–500 employees), Growing digital footprint.
The Goal: Gain visibility, defend against targeted phishing, and meet basic compliance obligations.
Your company now has more data, more employees, and perhaps regulatory requirements (like HIPAA or PCI). You are becoming a more attractive target. At this stage, passive defense isn't enough; you need visibility into what's happening on your network.
Add These Tools to Level 1:
- Secure Email Gateway (SEG):
- Over 90% of attacks start with email. A dedicated SEG filters out advanced phishing attempts, malicious attachments, and CEO fraud impersonation before they reach the employee's inbox.
- The Function: Advanced filtering and sandboxing for email traffic.
- Next-Generation Firewall (NGFW) / DNS Filtering:
- You need to control traffic leaving your network. If an employee accidentally clicks a malicious link, DNS filtering stops the computer from connecting to the hacker's server.
- The Function: Perimeter defense and web content filtering.
- Vulnerability Scanning:
- You can't fix what you don't know is broken. Automated scanners regularly check your network and external-facing applications for outdated software or misconfigurations that hackers could exploit.
- The Function: Proactively identifies security gaps.
- Security Awareness Training:
- Your technology stack is getting stronger, so attackers will target your people. Regular training and simulated phishing tests turn your employees from liabilities into a layer of defense.
- The Function: Reduces human error through education.
Level 3: The Advanced Stack (The "Run" Phase)
Target Audience: Enterprises, Heavily regulated industries, Dedicated security teams (SOC).
The Goal: Rapid detection, coordinated response, threat hunting, and "Zero Trust."
At this level, you assume you will be breached. The focus shifts from purely preventative measures to how quickly you can detect an intruder and kick them out before they cause damage. This requires centralization and automation.
Add These Tools to Levels 1 & 2:
- SIEM (Security Information and Event Management):
- This is the central brain of the advanced stack. It collects logs from every other tool mentioned (EDR, Firewall, Email) and correlates them to find patterns indicating a complex attack.
- The Function: Centralized log management and real-time alert correlation.
- SOAR (Security Orchestration, Automation, and Response):
- Alert fatigue kills security teams. SOAR automates repetitive tasks. For example, if the SIEM detects a phishing email, SOAR can automatically delete it from all inboxes and block the sender without human intervention.
- The Function: Automates incident response workflows.
- Identity and Access Management (IAM) / PAM:
- Moving beyond simple passwords to granular control. Who has access to what, and for how long? Privileged Access Management (PAM) specifically locks down high-level admin accounts that attackers covet most.
- The Function: Enforces "Least Privilege" and Zero Trust principles.
The Glue: Integration and Overlap
A common mistake in growing companies is buying "best-of-breed" tools that don't talk to each other. This creates silos of information.
When building your stack, integration is key. Your EDR should feed data to your SIEM. Your SIEM should trigger actions in your Firewall.
The Danger of Overlap:
Be wary of buying redundant tools. Many modern EDR platforms now include vulnerability scanning features. Many email providers (like Microsoft 365) have built-in security gateways that may be sufficient for Level 2 companies.
Always audit the capabilities of the tools you already own before buying something new.
Contact
Missing something?
Feel free to request missing tools or give some feedback using our contact form.
Contact Us