08
The 4 Biggest Cyber Threats and The Tools That Crush Them
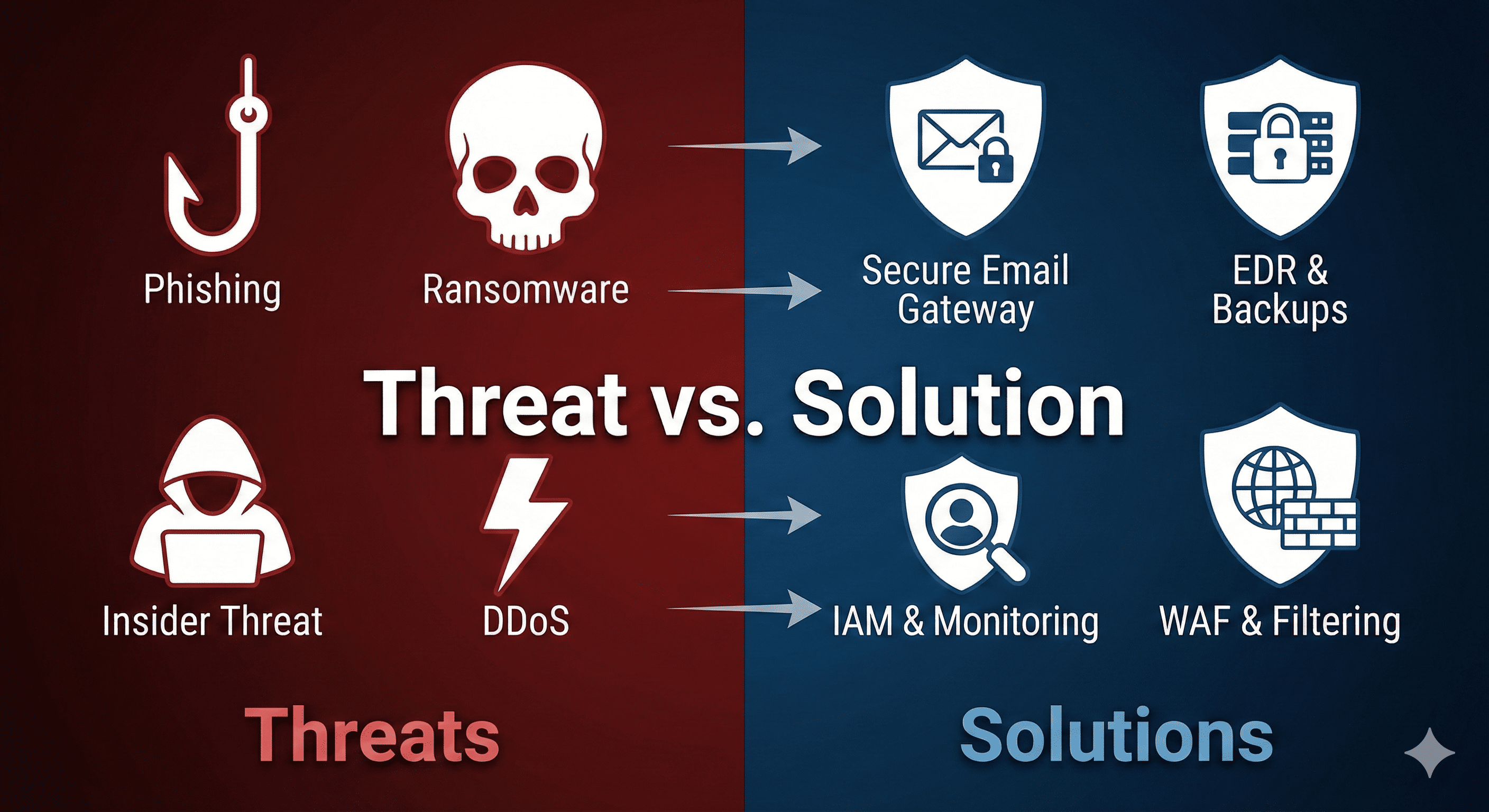
A practical guide mapping the four most dangerous cybersecurity threats (Phishing, Ransomware, Insider Threats, DDoS) directly to the specific tools that stop them. Perfect for business leaders looking to build a "Defense in Depth" strategy.
The 4 Biggest Cyber Threats & The Tools That Crush Them
In cybersecurity, fear is useful—but only if it leads to action. Reading about headlines of data breaches is scary, but it’s far more productive to understand exactly how those breaches happen and what specific technology stops them.
Cyber attacks aren't magic; they are mechanical processes. And for every method of attack, there is a counter-measure designed to break it. Here is a breakdown of the four most common threats facing organizations today, and the exact tools you need to neutralize them.
1. Phishing Attacks
The Threat:
Phishing remains the #1 delivery method for cyber attacks. It isn't a "hack" in the traditional sense; it's a con game. Attackers send fraudulent emails pretending to be a boss, a vendor, or a bank to trick employees into clicking a malicious link or downloading an infected attachment.
The Solution: Secure Email Gateways (SEG)
While training employees is important, human error is inevitable. You need a safety net. A Secure Email Gateway sits between the internet and your employee's inbox. It scans every incoming email for malicious links, dangerous attachments, and signs of impersonation (like a fake domain name) and quarantines them before the user ever sees them.
- Key Features: URL rewriting (scanning links even after delivery), sandboxing (testing attachments in a safe zone), and impersonation analysis.
- Top Tools: Proofpoint, Mimecast, Microsoft Defender for Office 365.
2. Ransomware
The Threat:
Ransomware is digital extortion. Once it enters your network, it moves laterally, finds your sensitive files, and encrypts them. The attacker then demands payment to provide the decryption key. If you don’t pay, you lose your data forever (or they leak it publicly).
The Solution: EDR + Immutable Backups
This threat requires a one-two punch.
- Endpoint Detection and Response (EDR): Unlike old antivirus which looked for "files," EDR looks for behaviors. If a program starts encrypting files rapidly, EDR kills the process immediately.
- Immutable Backups: If the defense fails, backups are your get-out-of-jail-free card. "Immutable" means the backups are read-only—even if the hacker gets admin rights, they cannot delete or encrypt your backups.
- Top EDR Tools: CrowdStrike Falcon, SentinelOne.
- Top Backup Tools: Veeam, Acronis, Datto.
3. Insider Threats
The Threat:
Not all attacks come from the outside. An "insider threat" could be a disgruntled employee stealing client lists before quitting, or a well-meaning employee accidentally granting public access to a private server. These are hard to catch because the user has valid credentials.
The Solution: IAM & UEBA
You need to control who has access and watch what they do with it.
- Identity and Access Management (IAM): Ensures users only have access to the specific files they need (Least Privilege), and revokes access instantly when they leave.
- User and Entity Behavior Analytics (UEBA): This uses AI to learn "normal" behavior. If Bob from Accounting usually downloads 10MB of data a day, but suddenly downloads 50GB at 3:00 AM on a Sunday, UEBA flags it as an anomaly.
- Top Tools: Okta (IAM), Splunk or Exabeam (UEBA).
4. DDoS Attacks
The Threat:
A Distributed Denial of Service (DDoS) attack aims to overwhelm your website or network with a flood of fake traffic, knocking you offline. It’s like a traffic jam effectively shutting down the highway to your store.
The Solution: Web Application Firewalls (WAF)
A WAF sits in front of your website like a bouncer. It inspects incoming traffic and filters out the "bad" bots while letting legitimate customers through. Modern WAFs use vast global networks to "absorb" the flood of traffic so your actual servers don't crash.
- Key Features: Rate limiting, IP reputation filtering, and managed rulesets for common attacks.
- Top Tools: Cloudflare, AWS Shield, Akamai.
Conclusion
Cybersecurity isn't about buying a "magic box" that fixes everything. It's about mapping tools to specific problems. By covering your bases—Email, Endpoints, Identity, and Network traffic—you build a defense that forces attackers to look for an easier target elsewhere.
Contact
Missing something?
Feel free to request missing tools or give some feedback using our contact form.
Contact Us